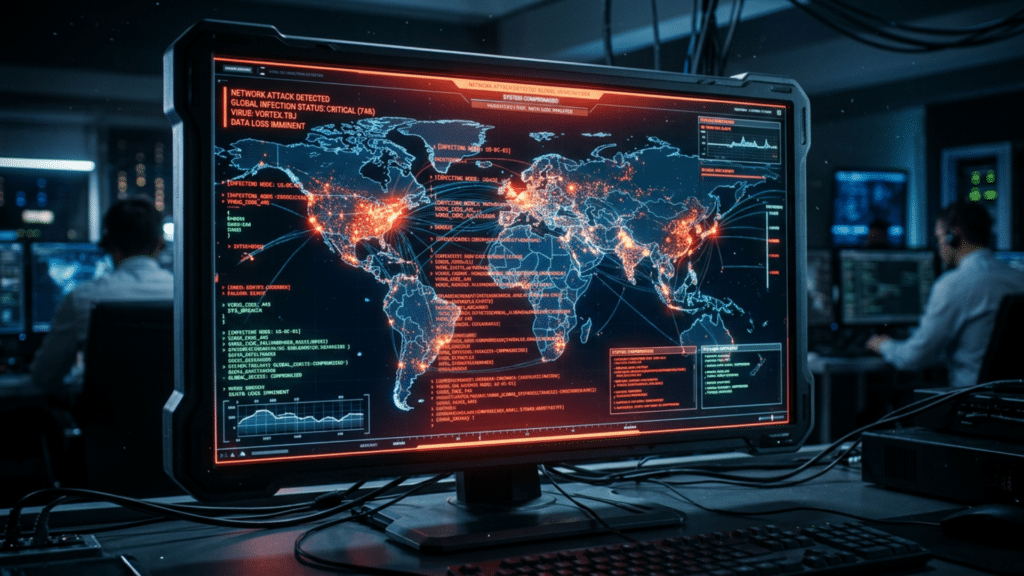
Computers were once seen as stable and predictable machines. That view began to shift as hidden threats appeared within growing digital networks.
Early virus attacks showed how easily small pieces of code could spread and disrupt entire systems.
These events forced people to rethink trust in technology and take security more seriously. Over time, each major incident shaped new ways to defend data and prevent damage.
The history of computer viruses reflects a turning point in how technology is built, used, and protected in an increasingly connected world.
What is a Computer Virus?
A computer virus is a type of malicious software designed to spread from one system to another. It attaches itself to files or programs and activates when those files are opened or run.
Once active, it can copy itself, damage data, slow down performance, or disrupt normal operations.
Many viruses spread through email attachments, downloads, or infected websites. They often rely on user action to begin spreading.
Over time, computer viruses have become more advanced, making them harder to detect and remove without proper security tools.
A Brief History of Computer Viruses
Computer viruses did not appear overnight. Their roots go back to early experiments with self-replicating code in the 1970s.
One of the first examples was the Creeper program, which moved across networks as a test. In the 1980s, viruses like Elk Cloner and Brain began spreading through floppy disks, reaching personal computers.
By the 1990s, email and the growing internet made it easier for viruses to spread quickly. In the 2000s, attacks became more serious, targeting businesses and global systems.
Over time, computer viruses shifted from simple experiments to powerful tools capable of causing widespread damage.
How Computer Viruses Cause Damage

Computer viruses can harm systems in many ways, often causing both technical and financial problems. Here are some common types of damage they cause:
- Data Loss or Corruption: Viruses can delete files, change data, or make important information unusable.
- System Slowdowns: Infected computers often run more slowly because the virus uses system resources in the background.
- Unauthorized Access: Some viruses allow hackers to access personal or sensitive information without permission.
- Network Disruption: Viruses can spread across networks, causing systems to crash or become unavailable.
- Financial Damage: Businesses may incur losses from downtime, repairs, or stolen financial data.
- Security Weaknesses: Viruses can create backdoors, making it easier for future attacks.
Most Famous Computer Viruses in History
Many computer viruses have left a lasting mark on technology and security. Below are 17 of the most famous computer viruses in history and why they still matter today:
1. Creeper Virus (1971)
Creeper is often considered the first computer virus. It was created as an experiment on ARPANET, an early network system.
Instead of damaging computers, it displayed a message and moved between systems. Its real impact was conceptual. It showed that programs could spread across networks without user control, raising early concerns about security and system vulnerability.
2. Elk Cloner (1982)
Elk Cloner spread through infected floppy disks and targeted Apple II computers. When a disk was used, the virus copied itself and displayed a short poem on the screen.
While not destructive, it spread widely among personal computers. It showed that viruses could easily spread through physical media and reach everyday users, not just large systems.
3. Brain Virus (1986)
Brain was the first virus to target IBM-compatible personal computers. It infected the boot sector of floppy disks, activating when the system started.
It spread quietly and was difficult to detect at the time. Its creators claimed it was meant to protect software, but it raised serious concerns about unauthorized access and data security in early computing.
4. Morris Worm (1988)
The Morris Worm was one of the first major internet-wide attacks. It spread through vulnerabilities in Unix systems and quickly grew out of control due to a coding flaw.
Thousands of computers slowed down or crashed. This incident highlighted the risks of connected networks and led to the creation of the first cybersecurity response teams.
5. Melissa Virus (1999)
Melissa spread through email attachments disguised as important documents. Once opened, it sent copies of itself to the user’s contacts in the address book.
This caused email systems to overload and shut down. Major companies were affected, and the damage was significant. It showed how human behavior, such as opening attachments, can contribute to virus spread.
6. ILOVEYOU Virus (2000)
The ILOVEYOU virus spread through emails with a simple subject line that encouraged users to open it. Once activated, it overwrote files and sent itself to contacts.
It spread rapidly across the world and caused billions in damage. Its success came from social engineering, proving that trust and curiosity could be used to launch large-scale cyberattacks.
7. Code Red (2001)
Code Red targeted Microsoft web servers by exploiting a software vulnerability. It spread automatically without user action and infected hundreds of thousands of systems quickly.
The virus launched attacks on websites, including government platforms. It demonstrated how automated threats could cause widespread disruption in a short time.
8. Nimda Virus (2001)
Nimda was unique because it spread in multiple ways, including email, infected websites, and shared networks. This made it extremely fast and difficult to control.
It affected both users and servers, causing widespread system failures. Nimda showed how combining different attack methods could make viruses far more effective and damaging.
9. SQL Slammer (2003)
SQL Slammer spread by exploiting a flaw in Microsoft SQL Server software. It moved extremely fast, infecting thousands of systems within minutes.
The virus caused major internet slowdowns and disrupted services like banking and airline systems. It highlighted how unpatched software can lead to sudden, large-scale network failures.
10. Blaster Worm (2003)
Blaster targeted Windows computers by using a known system vulnerability. It caused infected machines to crash and restart repeatedly, making them difficult to use.
The virus also attempted to launch attacks on Microsoft’s servers. It showed how ignoring system updates could leave computers open to serious threats.
11. Sobig Virus (2003)
Sobig spread through email and created massive amounts of spam. It infected millions of computers and overloaded networks with traffic.
The virus also turned infected systems into tools for sending more spam. It showed how viruses could be used for profit-driven activities, not just disruption or damage.
12. Mydoom (2004)
Mydoom became one of the fastest-spreading email worms in history. It created a large network of infected computers and launched distributed denial-of-service (DDoS) attacks.
These attacks slowed down internet traffic worldwide. Its scale and speed demonstrated how coordinated attacks could impact global communication systems.
13. Zeus Trojan (2007)
Zeus was designed to steal sensitive financial data, especially banking information. It worked by recording keystrokes and capturing login details.
The virus infected millions of computers and caused major financial losses. Zeus marked a shift toward targeted cybercrime, focusing on stealing money rather than simply causing damage.
14. Conficker (2008)
Conficker spread by exploiting weaknesses in Windows. It infected millions of computers and created large botnets that attackers could remotely control.
These networks could be used for various malicious activities. Conficker showed how large-scale infections could be organized and controlled over long periods.
15. Stuxnet (2010)
Stuxnet was a highly advanced virus that targeted industrial control systems, especially in nuclear facilities. It damaged physical equipment while remaining hidden from operators.
Many experts believe it was created by nation-states. Stuxnet marked a turning point, showing that cyberattacks could have real-world physical consequences.
16. WannaCry (2017)
WannaCry was a ransomware attack that locked users out of their files and demanded payment. It spread rapidly through network vulnerabilities, affecting hospitals, businesses, and governments.
Many systems were forced to shut down. The attack showed the global impact of ransomware and the importance of timely software updates.
17. NotPetya (2017)
NotPetya appeared to be ransomware but was designed to destroy data rather than recover it. It spread quickly through networks and caused massive damage to global companies.
Businesses faced long outages and financial losses. It demonstrated how cyberattacks could be used for large-scale disruption rather than for financial gain.
The Impact of These Viruses on Cybersecurity
Major virus outbreaks did more than cause damage. They forced a complete shift in how cybersecurity is understood and applied today. Each incident exposed weaknesses in systems and pushed the industry to strengthen defenses.
- Rise of Antivirus Software: Early attacks led to the development of antivirus programs that could detect and remove threats before they spread further.
- Regular System Updates: Many viruses exploit outdated software. This made regular updates and security patches a standard practice for both users and companies.
- Stronger Network Security: Firewalls, intrusion detection systems, and monitoring tools became more advanced to prevent large-scale attacks.
- Focus on User Awareness: Many viruses spread through human actions. This led to better training and awareness about suspicious emails, links, and downloads.
- Growth of Cybersecurity Industry: The increasing threat of attacks created demand for cybersecurity professionals, tools, and global security standards.
- Shift Toward Proactive Defense: Instead of reacting after attacks, organizations now focus on preventing threats before they happen.
- Government and Global Involvement: Large-scale attacks prompted governments to adopt policies, laws, and collaborations to address cyber threats more effectively.
Common Patterns Behind These Viruses
Many of these viruses may seem different, but they often follow similar patterns. These shared behaviors explain why they spread so quickly and caused such widespread damage.
Use of System Vulnerabilities
Many viruses exploit weaknesses in software or operating systems. When systems are not updated, these gaps become easy entry points. Attackers exploit these flaws to gain access and spread the virus with minimal user interaction.
Rapid Self-Replication
A key trait of most viruses is their ability to replicate rapidly. Once inside a system, they spread to other files, devices, or networks. This rapid replication enables them to infect large numbers of systems quickly.
Reliance on User Action
Many viruses depend on users opening attachments, clicking links, or downloading infected files. This makes human behavior a major factor in how viruses spread, especially in email-based attacks.
Multiple Methods of Spread
Some viruses use more than one way to infect systems. They may spread through email, websites, and shared networks at the same time. This makes them harder to stop and more effective.
Hidden or Delayed Activation
Many viruses remain hidden after entering a system. They may activate later, making detection difficult. This delay allows them to spread further before causing noticeable damage.
Creation of Backdoors
Some viruses create hidden access points in infected systems. These backdoors allow attackers to return later, steal data, or launch new attacks without being noticed.
Targeting Large Networks
Viruses often target systems connected to large networks, such as business or government systems. This increases their impact and allows them to spread more widely and quickly.
How to Protect Your Computer Today
Protecting your computer today requires a mix of good habits and basic security tools. These simple steps can reduce the risk of virus infections and keep your system safe:
- Keep Software Updated: Install updates for your operating system and apps regularly to fix security weaknesses.
- Use Reliable Antivirus Software: A trusted antivirus program can detect and remove threats before they cause damage.
- Avoid Suspicious Links and Emails: Do not open unknown attachments or click on links from untrusted sources.
- Download from Trusted Sources Only: Install software only from official websites or verified platforms.
- Use Strong Passwords: Create complex passwords and avoid reusing the across multiple accounts.
- Enable Firewalls: Firewalls help block unauthorized access to your system and network.
- Back Up Important Data: Regular backups ensure your files are safe if your system gets infected.
- Be Careful with Public Wi-Fi: Avoid accessing sensitive information on unsecured networks.
Conclusion
Computer viruses show how fragile digital systems can be when small gaps are ignored. Each case reflects a turning point that forced better thinking, stronger design, and smarter responses.
These events did not just cause damage; they influenced long-term decisions in technology and security.
Awareness is one of the strongest defenses available. Keep paying attention to how risks evolve, and take simple steps to stay secure.
For more insights like this, continue reading and stay informed about the changing world of cybersecurity.
Frequently Asked Questions
What is the First Thing You Should Change if You are Hacked?
The first thing to change is your passwords, especially for email and banking accounts. Use strong, unique passwords and enable two-factor authentication to secure access immediately.
Does Shutting Down a Computer Stop Hackers?
Shutting down can temporarily stop active connections, but it does not remove malware. Hackers may regain access once the system is turned back on if threats remain.
Can Hackers Access My Computer if it is Turned Off?
A powered-off computer cannot be accessed remotely. However, if malware is already installed, it may become active again once the system is turned on and connected to the internet.