Cybersecurity compliance sounds like something only big corporations worry about. But in today’s digital world, one wrong move can expose your business, your customers, and your reputation overnight.
The rules exist for a reason, and the businesses that ignore them rarely get a second chance.
Understanding cybersecurity compliance isn’t just smart; it’s survival. Stick around, because what you’re about to learn might be the most important thing you read this year.
What Is Cybersecurity Compliance?
Cybersecurity compliance means following security rules and standards set by governments or industry groups.
These rules are designed to protect sensitive data, keep personal information private, and ensure businesses operate securely.
Consider it an essential safety checklist for every organization to follow to ensure everyone’s safety.
If you’re a small business or a large corporation, meeting these standards helps prevent costly data breaches and shows customers that their information is in safe hands.
Key Cybersecurity Compliance Requirements
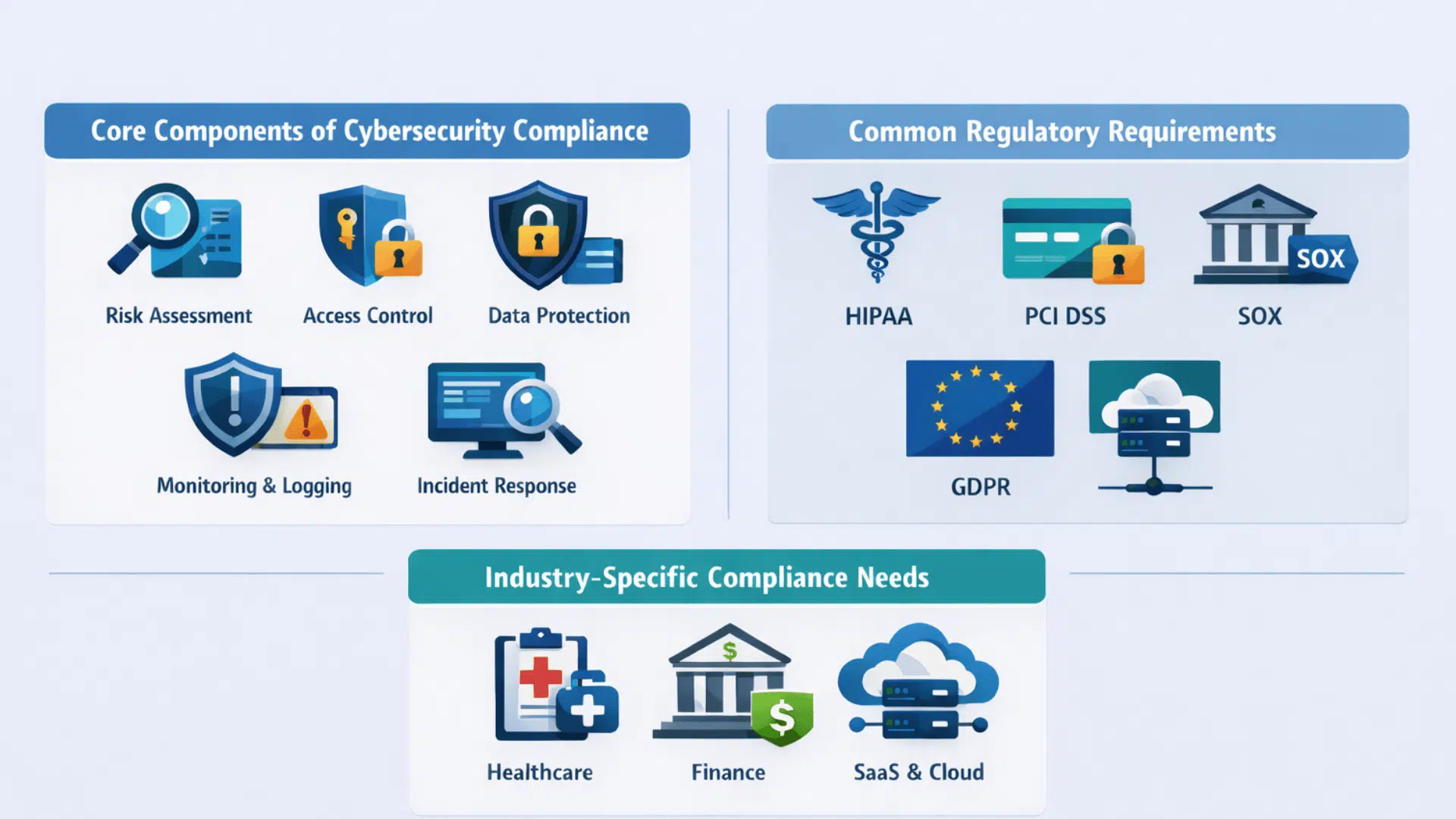
Cybersecurity compliance involves core practices, regulations, and sector needs, shaping what “compliant” means for your business.
1. Core Components of Cybersecurity Compliance
Every compliance program, regardless of industry, is built on the same foundational pillars. These components form the baseline every business must address before tackling specific frameworks.
- Risk Assessment: Regularly identify and evaluate threats to your systems, data, and operations before they escalate into serious incidents.
- Access Control: Limit who can access sensitive data and systems, using role-based permissions and multi-factor authentication to reduce exposure.
- Data Protection: Encrypt sensitive information both in storage and in transit, ensuring unauthorized parties can never read or misuse it.
- Monitoring and Logging: Track system activity continuously to flag suspicious behavior quickly and investigate it before damage spreads.
- Incident Response: Have a documented plan ready to contain, address, and recover from security breaches with minimal disruption.
2. Common Regulatory Requirements
The US regulatory landscape includes major frameworks businesses must understand based on industry and customer base. Ignoring them is risky and can lead to legal and financial consequences.
- HIPAA: Protects patient health information and applies to healthcare providers, insurers, and their business associates handling medical data.
- PCI DSS: Required for any business that processes, stores, or transmits payment card data, setting strict security standards for transactions.
- SOX: Applies to publicly traded companies, requiring strong internal controls over financial data and IT systems that support reporting.
- GDPR: Governs how businesses collect and handle data belonging to EU residents, regardless of where the business itself is located.
3. Industry-Specific Compliance Needs
Beyond general frameworks, certain industries carry unique compliance obligations shaped by the sensitivity of their data and the nature of their operations. Understanding your sector’s specific requirements is critical to building a complete program.
- Healthcare: Must meet HIPAA standards for patient data privacy, with strict rules around electronic health records, access logs, and breach notifications.
- Finance: Faces overlapping obligations under SOX, GLBA, and state-level regulations, requiring tight controls over financial data and customer information.
- SaaS and Cloud: Must address data residency, shared responsibility models, and vendor compliance, as cloud environments introduce unique risks that traditional frameworks don’t always cover.
Key Cybersecurity Compliance Frameworks and Regulations
Framework relevance depends on your industry, location, and data type. Focus on what directly impacts your compliance needs.
| FRAMEWORK | BEST FOR | KEY FOCUS |
|---|---|---|
| GDPR | Global businesses handling EU data | Data privacy, user rights |
| HIPAA | Healthcare | ePHI protection |
| PCI DSS | E-commerce, retail | Payment security |
| NIST CSF | All industries | Risk management |
| SOC 2 | SaaS, tech | Trust criteria |
| ISO 27001 | Enterprises | ISMS, governance |
| CMMC 2.0 | Defense contractors | DoD data security |
| CCPA/CPRA | US (California) | Consumer privacy |
| NIS2/DORA | EU-facing firms | Resilience, risk |
How to Achieve Cybersecurity Compliance: A Step-by-Step Guide

Compliance doesn’t happen overnight, but clear steps make it manageable. The goal isn’t perfection from day one; it’s building a consistent system that grows stronger over time.
Step 1: Identify Which Regulations Apply to You
Your industry and location decide your rules. Healthcare businesses follow HIPAA, payment processors follow PCI DSS, and anyone serving EU customers must meet GDPR requirements.
Getting this wrong from the start means building your entire compliance program on the wrong foundation.
Step 2: Conduct a Risk Assessment
Identify your sensitive data and evaluate how it’s stored, accessed, and protected. This helps you spot vulnerabilities before they become costly problems.
Understanding where your risks are located is essential; without that knowledge, taking the next step can feel like guesswork. Knowing this helps you make more confident and informed decisions.
Step 3: Perform a Compliance Gap Analysis
Compare your current security controls against what your framework requires. Check network configurations, access permissions, third-party relationships, and endpoint devices at least once a year.
The gaps you find here become your compliance roadmap going forward.
Step 4: Implement Access Controls
Give users access only to what they need. Combine the Least Privilege Principle, Multi-Factor Authentication, and Role-Based Access Control to keep sensitive systems secure.
Even just one overly privileged account can easily become a target for attackers. It’s important to ensure all accounts are properly secured to keep everyone safe.
Step 5: Train Your Employees
Human error is the top cause of breaches. Regularly train staff on phishing, data handling, and incident reporting, and enforce clear consequences for policy violations.
Having a well-trained team is often your most reliable and budget-friendly way to protect your interests.
Step 6: Monitor, Audit, and Improve Continuously
Use automated alerts and log monitoring to catch threats early. Schedule annual audits, update policies regularly, and test your incident response plan through simulated attacks.
Compliance isn’t a one-time achievement; it’s an ongoing commitment that evolves with your business.
Top Challenges Businesses Face with Cybersecurity Compliance
Compliance sounds straightforward on paper, but the reality is far messier. Businesses of all sizes hit real roadblocks that make staying compliant genuinely difficult.
- Overlapping Frameworks: GDPR, HIPAA, and CMMC each have conflicting requirements, creating serious confusion.
- Resource Constraints: Most SMBs lack the staff and budget to maintain a proper compliance program.
- Regulatory Change: Rules evolve constantly, and falling behind unknowingly puts businesses at risk.
- Jurisdictional Conflicts: Operating across regions means navigating laws that rarely align neatly.
- Compliance vs. Security: Meeting minimum audit requirements doesn’t always mean you’re genuinely protected.
Tools That Help Automate and Maintain Cybersecurity Compliance
Compliance tools vary based on business size and complexity. The right stack helps automate processes, reduce risk, and stay audit-ready without excessive manual effort.
| TOOL CATEGORY | BEST FOR | KEY FUNCTION |
|---|---|---|
| GRC Platforms | Enterprises, regulated industries | Centralized risk and compliance management |
| SIEM Tools | Security teams | Real-time monitoring and threat detection |
| Compliance Software | SMBs to enterprises | Audit tracking, policy management |
| vCISO Services | SMBs | Strategic security leadership |
| AI Compliance Tools | Growing businesses | Automation, predictive risk insights |
Wrapping It Up
Cybersecurity compliance isn’t a destination; it’s a continuous venture that demands attention, action, and accountability.
Thriving businesses aren’t just tech-driven; they take obligations seriously and stay ahead of threats.
Start small, build consistently, and treat every step as progress. Your customers trust you with their data. Cybersecurity compliance is simply how you prove that trust is well placed.
Frequently Asked Questions(FAQ)
What Happens If a Business Fails to Meet Cybersecurity Compliance Requirements?
Non-compliance triggers heavy fines, legal action, and lasting reputational damage. Regulators take violations seriously, and lost customer trust is often the hardest thing to rebuild.
How Often Should a Company Update Its Cybersecurity Compliance Program?
Review your program at least annually or after any major system change. Regulations evolve constantly, and staying current is just as important as the initial setup.
Is Cybersecurity Compliance the Same for Small Businesses and Large Enterprises?
Core requirements are similar, but small businesses face steeper challenges due to limited resources. Regulators offer no exemptions based on size, making compliance equally critical for everyone.
Which Cybersecurity Compliance Framework Should a New Business Start With?
The right framework depends on your industry, location, and data type. Always start with a risk assessment before committing to any specific framework.