Cyber risk is a growing concern for organizations of all sizes. As digital systems expand, the need to manage threats becomes more urgent.
Many companies struggle to translate technical risks into clear business impact. This gap makes planning and communication difficult.
Cyber risk quantification aims to solve this by adding structure to risk assessment. It connects cybersecurity with real-world outcomes.
This approach is gaining attention across industries. A clear understanding can support better decisions and stronger risk management over time.
What is Cyber Risk Quantification (CRQ)?
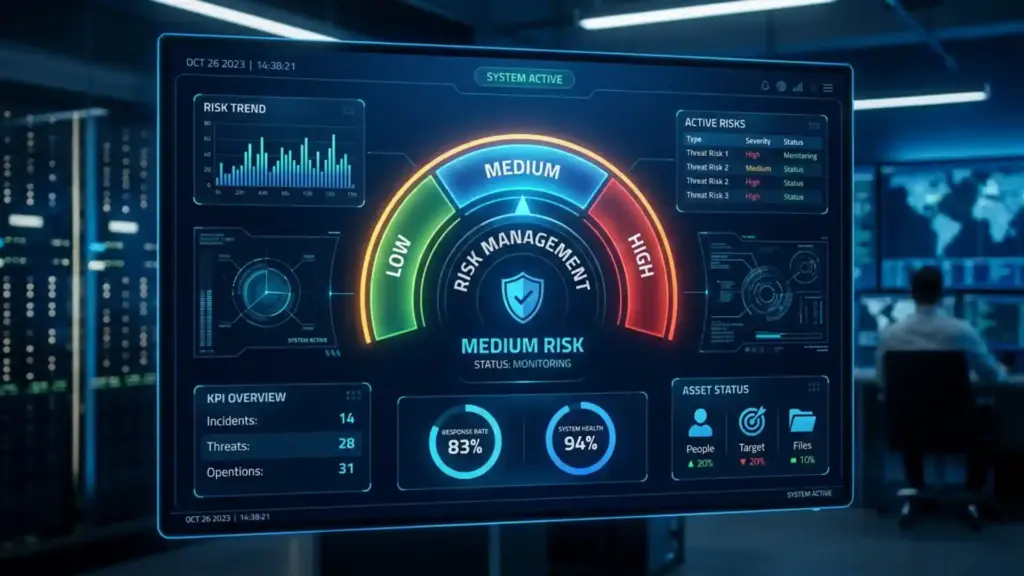
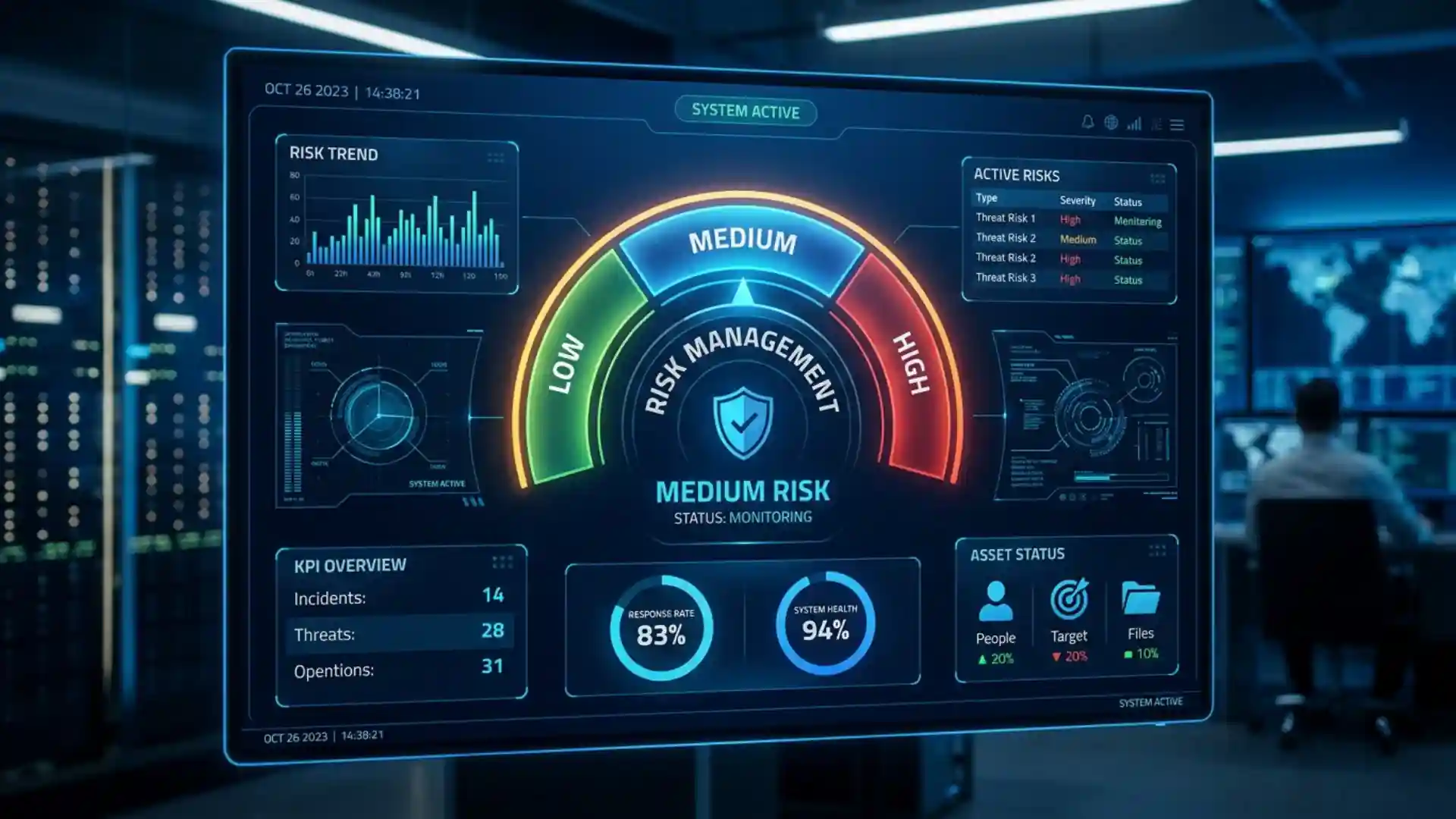
Cyber Risk Quantification (CRQ) is the process of measuring cyber risk numerically, often expressed in monetary terms. Instead of labeling risks as “high,” “medium,” or “low,” it assigns a clear estimate of potential loss.
This approach helps organizations understand the potential cost of a cyber incident.
It connects technical risks, such as data breaches or system failures, to real business impacts, including financial loss, downtime, or reputational damage.
CRQ uses data, models, and probability to estimate both the likelihood of an event and its possible impact. Turning risk into measurable figures allows teams to make more informed decisions about security investments and priorities.
Importance of Cyber Risk Quantification
Cyber risk quantification helps organizations understand cybersecurity risks in a practical, measurable way.
- Better Decision-Making: Helps leaders understand cyber risks in financial terms, making it easier to plan budgets and investments.
- Clear Communication: Creates a common language between technical teams and business leaders using measurable data.
- Improved Risk Prioritization: Identifies which threats pose the greatest risk, so teams can focus on what matters most.
- Stronger Business Alignment: Connects cybersecurity efforts with overall business goals and strategies.
- More Effective Risk Management: Replaces vague labels like “high” or “low” with clear, data-driven insights.
- Support for Cyber Insurance Decisions: Helps estimate potential losses, making it easier to choose the right insurance coverage.
- Justifies Security Spending: Provides clear reasoning for investments in cybersecurity tools and solutions.
How Cyber Risk Quantification Works
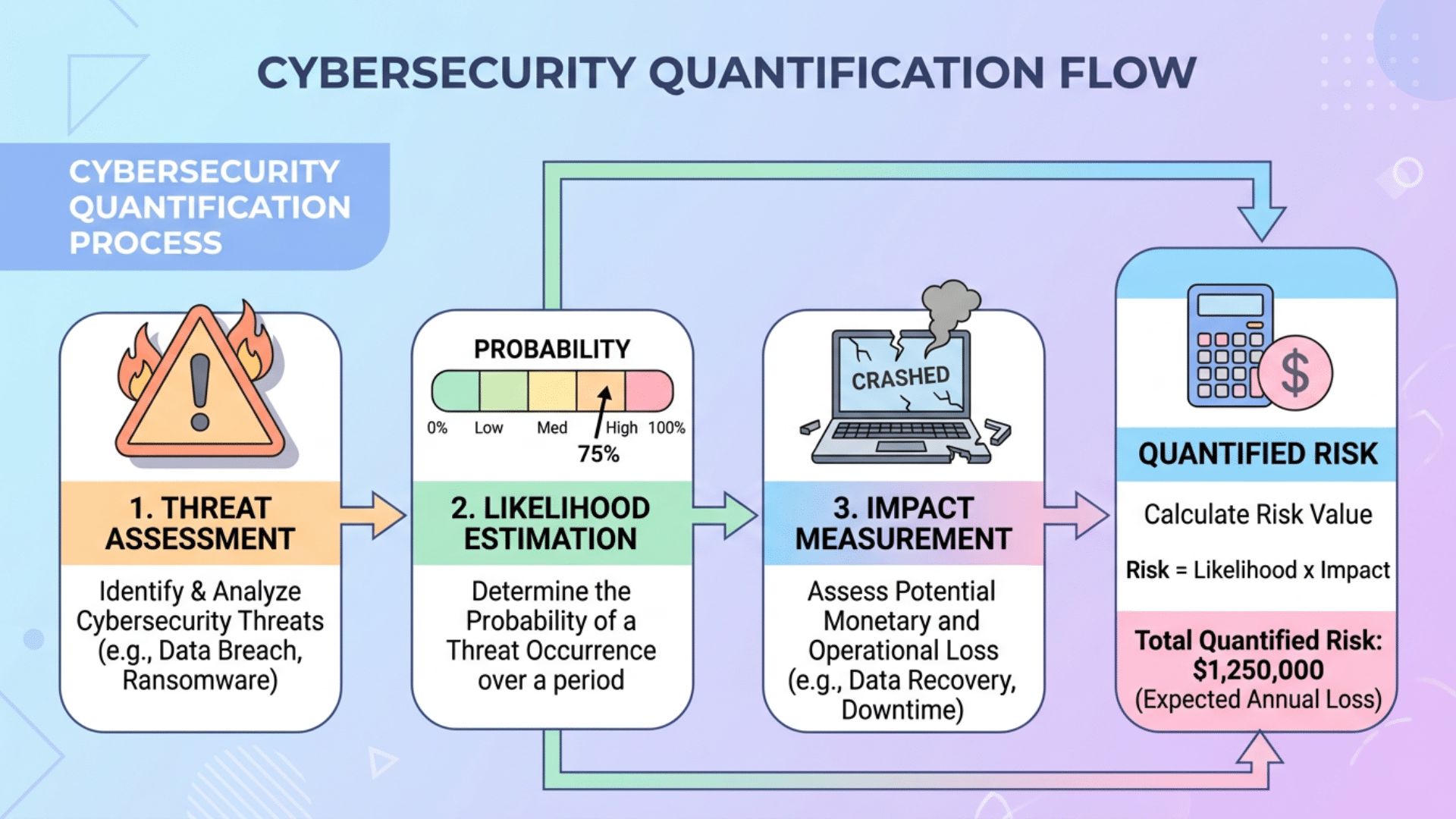
Cyber risk quantification follows a structured approach to turn cyber threats into measurable values.
It starts with risk identification, where organizations list possible threats such as data breaches or ransomware attacks.
The next step is likelihood estimation, where each risk is evaluated based on how often it might occur using available data and past incidents.
After that, the focus shifts to impact analysis. This involves estimating the potential damage, often in financial terms like recovery costs, lost revenue, or legal expenses.
Once both likelihood and impact are defined, organizations apply quantitative models to combine these factors into a clear risk value.
Finally, teams use this information to compare risks and guide decisions.
Main Cyber Risk Quantification Models
Cyber risk quantification relies on various models to measure risk in a structured, consistent way. Each model uses its own method to estimate likelihood and impact.
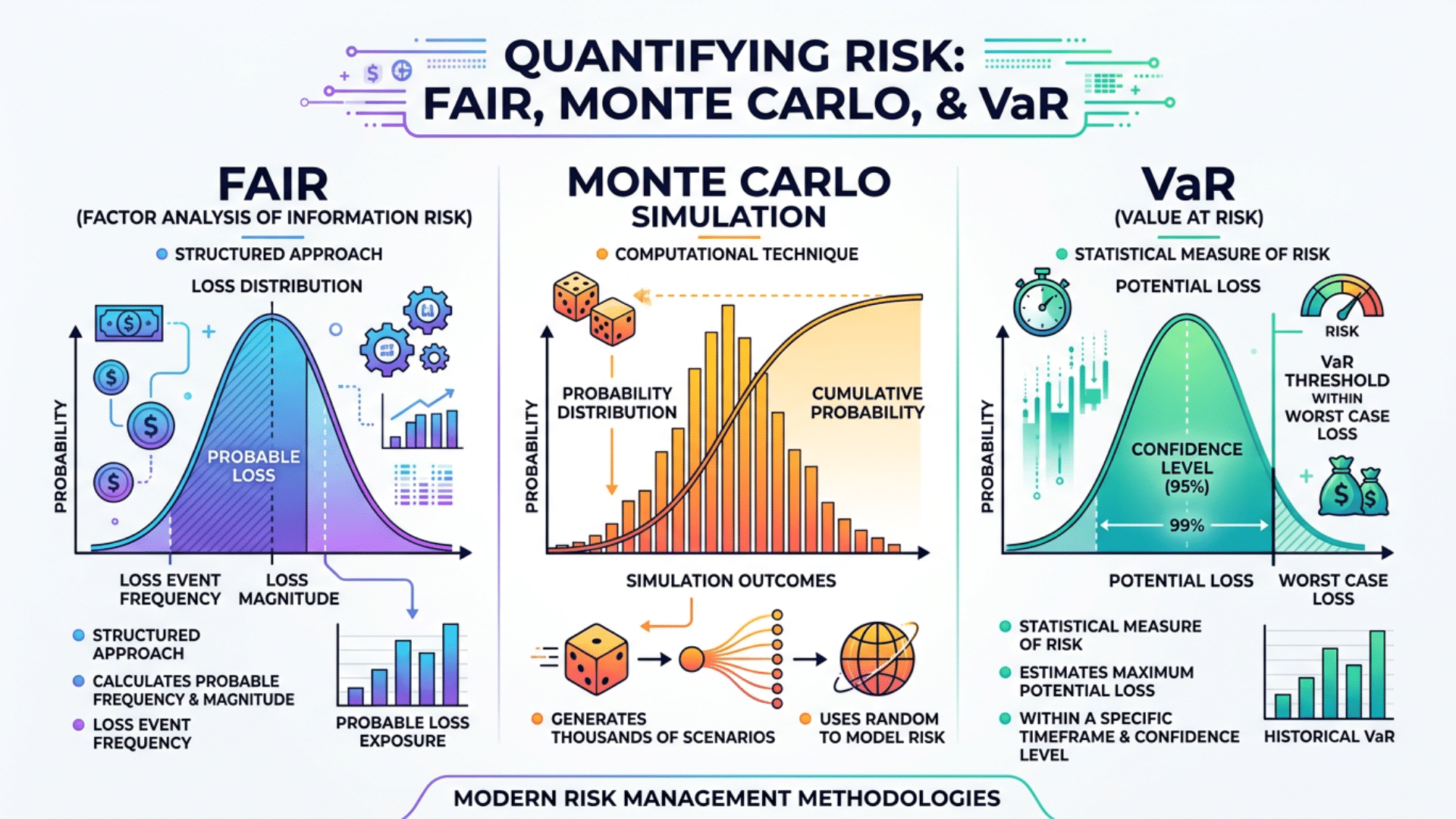
FAIR Model (Factor Analysis of Information Risk)
The FAIR model is one of the most widely used approaches for quantifying cyber risk. It breaks risk into two main parts: the likelihood of an event and the potential loss it could cause.
It also considers factors such as threat capability, control strength, and exposure. Because it focuses on financial outcomes, it helps organizations present risk in terms that business leaders understand and act on.
NIST-Based Risk Quantification
This approach builds on the NIST cybersecurity framework, which is widely adopted across industries. It follows a structured process to identify threats, assess vulnerabilities, and estimate impact.
While NIST is often seen as qualitative, many organizations extend it with quantitative methods to assign numerical values to risk. This makes it easier to align cybersecurity efforts with compliance and governance needs.
Monte Carlo Simulation
Monte Carlo simulation uses probability and repeated sampling to estimate possible risk outcomes. It runs thousands of scenarios based on different inputs, such as attack frequency and loss size. This produces a range of possible results rather than a single estimate.
It helps organizations understand uncertainty, including both expected losses and extreme scenarios with a low probability but high impact.
Value at Risk (VaR)
Value-at-Risk estimates the potential financial loss over a defined period at a given confidence level. For example, it can show the maximum expected loss within a year under normal conditions.
This model is widely used in finance and is applied to cyber risk to measure exposure. It gives leaders a clear figure to compare against budgets and risk tolerance levels.
Bayesian Models
Bayesian models rely on probability and continuous learning. They update risk estimates as new data becomes available, such as new threats or incident reports.
This makes them useful in fast-changing environments where risks evolve quickly. By adjusting predictions over time, these models offer a more flexible, adaptive approach to measuring cyber risk.
Cyber Risk Quantification Tools
Cyber risk quantification tools help organizations measure and report cyber risk in financial terms. They use models, data, and automation to turn complex threats into clear insights.
These tools gather data from sources like security systems, threat intelligence, and past incidents. They apply models such as FAIR to estimate risk and present results through dashboards and reports for leadership.
Common Cyber Risk Quantification Tools
- Safe Security (SAFE): Focuses on financial risk measurement and business insights
- CyberSaint: Offers risk tracking with executive-level reporting
- Axio: CRQ integrated with enterprise risk management (GRC-focused)
Key Features to Look For
- Data integration from multiple sources
- Scenario modeling and simulations
- Clear financial reporting
These tools make it easier to understand cyber risk and support better planning and investment decisions.
How Organizations Use Cyber Risk Quantification
Organizations use cyber risk quantification to support clear and practical decision-making across different areas.
- Budgeting and Investment Planning: Helps decide how much to spend on cybersecurity and where to invest for the best impact.
- Risk Prioritization: Identifies the most critical threats so teams can focus on reducing high-impact risks first.
- Cyber Insurance Decisions: Supports choosing the right coverage by estimating potential financial losses.
- Executive Communication: Translates technical risks into clear business terms for leadership understanding.
- Governance and Compliance: Aligns cybersecurity efforts with business goals and regulatory requirements.
- Strategic Planning: Helps organizations plan long-term security strategies based on measurable risk data.
How to Get Started with Cyber Risk Quantification
Getting started with cyber risk quantification is often simpler than it seems. A step-by-step approach helps build clarity and consistency over time.
Start with a Focused Risk Scenario
Begin by selecting one clear risk, such as a ransomware attack or data breach. This keeps the process simple and easier to manage.
Choose a Basic Model or Method
Select a simple approach that fits your current needs. It does not have to be complex, as the goal is to build a clear foundation.
Use Available Data
Rely on internal records, past incidents, and industry data to estimate how often a risk may occur and its potential impact.
Begin with Simple Tools
Start with basic tools like spreadsheets before moving to advanced cyber risk quantification tools as needed.
Improve Over Time
Refine your estimates and methods as more data becomes available, making your risk assessment more accurate and useful.
Challenges of Cyber Risk Quantification
Cyber risk quantification provides valuable insights, but organizations often face several practical challenges when applying it.
| Challenge | Explanation |
|---|---|
| Limited and Unreliable Data | Many organizations lack enough quality data to make accurate risk estimates. |
| Evolving Threat Landscape | Cyber threats change quickly, making it hard to keep models up to date. |
| Difficulty in Measuring Impact | The financial impact, especially reputational loss, is hard to quantify precisely. |
| Model Limitations | Each model has assumptions that may not fit every situation or organization. |
| Skill and Resource Gaps | Teams may lack the expertise or tools needed for proper risk quantification. |
| Uncertainty in Results | Risk estimates are not exact and always involve some level of uncertainty. |
Best Practices for Effective CRQ
To get the most value from cyber risk quantification, organizations should adopt a clear, consistent approach.
- Start Simple: Begin with a few key risks and basic methods before moving to more advanced models.
- Use Reliable Data: Base your estimates on internal data and trusted external sources for better accuracy.
- Focus on High-Impact Risks: Prioritize risks that could cause the most financial or operational damage.
- Keep Methods Consistent: Use the same approach across teams to ensure clear and comparable results.
- Update Regularly: Review and adjust risk estimates as new data and threats emerge.
- Align with Business Goals: Make sure cyber risk analysis supports the overall business strategy.
- Communicate Clearly: Present findings in simple terms so leadership can understand and act quickly.
Conclusion
Cyber risk quantification is becoming a practical way to bring structure to cybersecurity decisions. It shifts the focus from vague risk levels to clear, measurable outcomes that leaders can act on.
As organizations deal with growing digital exposure, having a method to evaluate risk in real terms can improve how they plan and respond.
The process does not need to be perfect from the start. What matters is building a consistent approach and improving it over time.
Start applying these ideas to strengthen how cyber risk is understood and handled.
Frequently Asked Questions
Is CRQ only for Large Companies?
No, CRQ can be used by organizations of any size. Smaller businesses can start with simple methods and scale as needed.
What Tools are Used for Cyber Risk Quantification?
Common tools include RiskLens, Safe Security, CyberSaint, and Balbix. Many organizations also begin with spreadsheets before moving to advanced platforms.
How Accurate is Cyber Risk Quantification?
CRQ provides estimates based on data and models, not exact predictions. Accuracy improves over time as better data and methods are used.