An IT security assessment plays a key role in keeping systems safe and reliable. Modern IT environments are complex, with multiple devices, users, and access points connected at all times.
This creates more chances for gaps to appear if systems are not reviewed regularly. Small issues can go unnoticed and turn into larger risks over time.
A clear and structured approach helps teams stay in control. It also supports better planning and stronger protection.
This guide provides a simple starting point for building a steady and effective security review process.
What is an IT Security Assessment?
An IT security assessment is a structured review of an organization’s technology environment to measure its security strength.
It focuses on identifying gaps in systems, configurations, and access controls that could pose risks.
This process examines how data is handled, who has access, and how systems respond to potential threats.
It also evaluates existing safeguards to see if they meet current security standards. The outcome is a clear view of where improvements are needed.
By using this insight, organizations can strengthen defenses, reduce exposure to threats, and align their security efforts with business needs and compliance requirements.
Why and When to Perform IT Security Assessments
IT security assessments help prevent major security issues by identifying risks early, before they lead to data breaches or system failures.
They also support compliance by ensuring systems meet industry standards and regulatory requirements. In addition, they improve decision-making by providing clear insight into areas that need attention.
Over time, they strengthen overall protection by keeping systems aligned with current security practices.
When to Perform IT Security Assessments
The timing of an assessment should follow a consistent and practical schedule. Common situations include:
- On a regular basis, Most organizations perform assessments annually or quarterly
- After major changes, Such as system upgrades, new tools, or cloud migrations
- After a security incident: To understand what went wrong and fix gaps
- When new threats emerge: To stay prepared against evolving risks
Regular assessments help maintain strong protection and ensure systems remain secure over time.
Key Steps in an IT Security Assessment Process
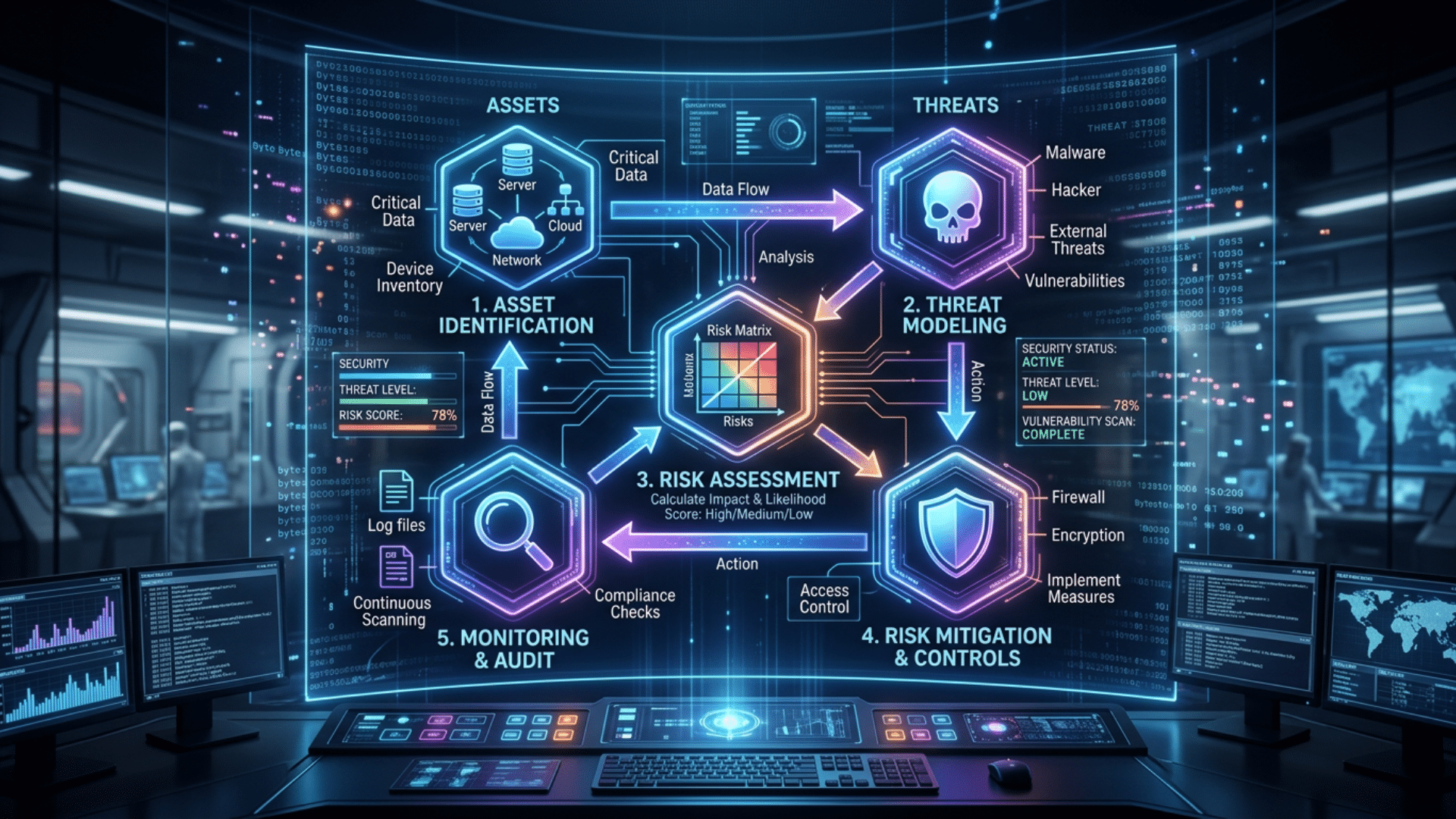
An IT security assessment is built around a few core components, including assets, threats, vulnerabilities, and risks. These elements form the foundation of the process and guide how each step is carried out.
Step 1: Define Scope and Objectives
Start by clearly defining what will be included in the assessment. This may involve specific systems, networks, applications, or data sets. It is also important to identify stakeholders and understand business priorities at this stage.
A well-defined scope prevents confusion, avoids wasted effort, and ensures the assessment focuses on the most critical areas.
Step 2: Identify and Classify Assets
Create a detailed inventory of all critical assets, including hardware, software, databases, and user accounts. This step should also include third-party services and cloud resources if they are part of the environment.
Once identified, classify assets based on their importance, sensitivity, and impact on operations. This helps determine which assets require stronger protection and closer monitoring.
Step 3: Identify Threats and Vulnerabilities
Review potential threats, including external attacks, insider risks, and system failures. At the same time, identify vulnerabilities like outdated software, weak authentication, or poor configurations.
Using tools like vulnerability scanners can help speed up this process. Understanding both threats and weaknesses provides a clearer picture of where systems are most exposed.
Step 4: Analyze and Evaluate Risks
Assess each risk by combining the likelihood of occurrence with its potential impact. This step often involves risk scoring to facilitate comparisons.
Consider how each risk could affect operations, data integrity, and user trust. A structured evaluation helps teams move beyond guesswork and focus on measurable risk levels.
Step 5: Prioritize Risks
Once risks are evaluated, rank them based on severity and urgency. High-impact and high-probability risks should be addressed first, especially those affecting critical systems or sensitive data.
Lower-level risks can be scheduled for later action. Clear prioritization ensures that resources are used effectively and urgent issues are not overlooked.
Step 6: Implement Security Controls
Apply appropriate controls to reduce or eliminate identified risks. This may include installing updates, strengthening access controls, enforcing security policies, or deploying tools like firewalls and intrusion detection systems.
The goal is to reduce risk to an acceptable level while maintaining system performance and usability.
Step 7: Document and Report Findings
Record all findings in a structured and easy-to-understand report. This should include identified risks, their impact, actions taken, and recommended next steps.
Clear documentation helps stakeholders understand the current security position and supports accountability. It also serves as a reference for future assessments.
Step 8: Monitor and Review Regularly
Security requires ongoing attention. Regular monitoring helps detect new issues early, while periodic reassessments ensure controls remain effective.
Systems, users, and threats change over time, so reviews should be scheduled consistently. A continuous approach helps maintain long-term security and reduces the chance of unexpected risks.
Tools and Methods Used in IT Security Assessments
IT security assessments rely on a mix of tools and methods to identify risks, test systems, and validate security controls. Each approach serves a specific purpose, and using them together provides a more complete and accurate view of the security environment.
| Tool / Method | Purpose | How It Is Used |
|---|---|---|
| Vulnerability Scanners | Identify known weaknesses in systems and software | Scan networks, applications, and devices for outdated software or misconfigurations |
| Penetration Testing | Simulate real-world attacks to test system defenses | Ethical hackers attempt to exploit vulnerabilities to assess actual risk |
| Security Audits | Review policies, procedures, and controls | Evaluate if security practices meet standards and compliance requirements |
| Configuration Reviews | Check system and network settings | Ensure configurations follow security best practices and are properly set |
| Log Analysis Tools | Monitor and analyze system activity | Review logs to detect unusual behavior or potential security incidents |
| Risk Assessment Tools | Evaluate and prioritize risks | Assign risk scores based on likelihood and impact |
| Interviews & Questionnaires | Gather insights from staff and stakeholders | Understand real-world usage, access issues, and security awareness |
| Network Scanning Tools | Map network structure and detect exposed services | Identify open ports, active devices, and possible entry points |
IT Security Assessment Frameworks to Know
IT security frameworks provide structured guidelines for performing assessments consistently and reliably. They help organizations follow proven methods, improve accuracy, and align with industry standards.
NIST Risk Management Framework (RMF)
The NIST RMF is widely used to manage security risks in a structured manner. It focuses on identifying risks, selecting appropriate controls, and continuously monitoring systems. It is commonly used by government agencies and large organizations.
This framework focuses on information security risk management and is part of the broader ISO 27000 family. It helps organizations identify, assess, and treat risks while staying aligned with international standards and compliance requirements.
FAIR (Factor Analysis of Information Risk)
FAIR is designed to measure risk in financial terms. It helps organizations understand the potential cost of security risks, making it easier to prioritize actions and justify security investments.
OCTAVE focuses on organizational risk and internal processes. It helps teams identify critical assets, evaluate risks, and develop security strategies aligned with business priorities rather than solely technical factors.
CIS Critical Security Controls
This framework provides a set of practical and prioritized security actions. It is useful for organizations that want clear, step-by-step controls to improve their overall security posture.
COBIT is focused on IT governance and management. It helps organizations align security efforts with business goals, manage risks effectively, and maintain compliance through structured processes.
Best Practices for Effective IT Security Assessment
Following best practices improves the accuracy and value of an IT security assessment. A thoughtful approach ensures the process is not only complete but also useful for real decision-making.
- Focus on what matters most: Prioritize critical systems, sensitive data, and high-impact risks instead of trying to cover everything
- Use a balanced approach: Combine automated tools with expert review to get both speed and accuracy
- Align with business needs: Security efforts should support operations, not work in isolation
- Maintain clear documentation: Well-organized records make it easier to track progress and repeat assessments
- Stay current with threats: Update your approach as new risks and technologies emerge
- Treat it as an ongoing process: Regular reviews are more effective than one-time assessments
Common Challenges and How to Avoid Them
IT security assessments can face several challenges that reduce their effectiveness. Addressing these issues early helps ensure more accurate and reliable results.
| Challenge | How to Avoid It |
|---|---|
| Incomplete asset visibility | Maintain a complete and regularly updated inventory of all systems and data |
| Lack of a clear scope | Define a focused scope based on critical assets and business priorities |
| Over-reliance on tools | Combine automated tools with manual review and expert analysis |
| Poor risk prioritization | Rank risks based on impact and likelihood to focus on key issues |
| Weak documentation | Use clear, structured reporting for all findings and recommendations |
| One-time assessment mindset | Schedule regular assessments and treat security as an ongoing process |
Final Thoughts
An effective IT security assessment is not just about completing a process. It is about building a clear understanding of where your systems stand today and what needs attention next.
Small gaps, when ignored, can turn into larger problems over time. A consistent and well-managed approach helps teams stay prepared and respond with confidence.
The real value comes from how findings are used to guide decisions and improve security over time.
Take the next step by reviewing your current approach and applying these practices to strengthen your IT environment starting today.