Security is a growing concern in homes, offices, and public spaces. Traditional methods such as keys and passwords are still widely used, yet they often fail to provide strong protection.
Lost keys and shared codes can easily lead to unauthorized access. As a result, many systems are shifting toward smarter solutions.
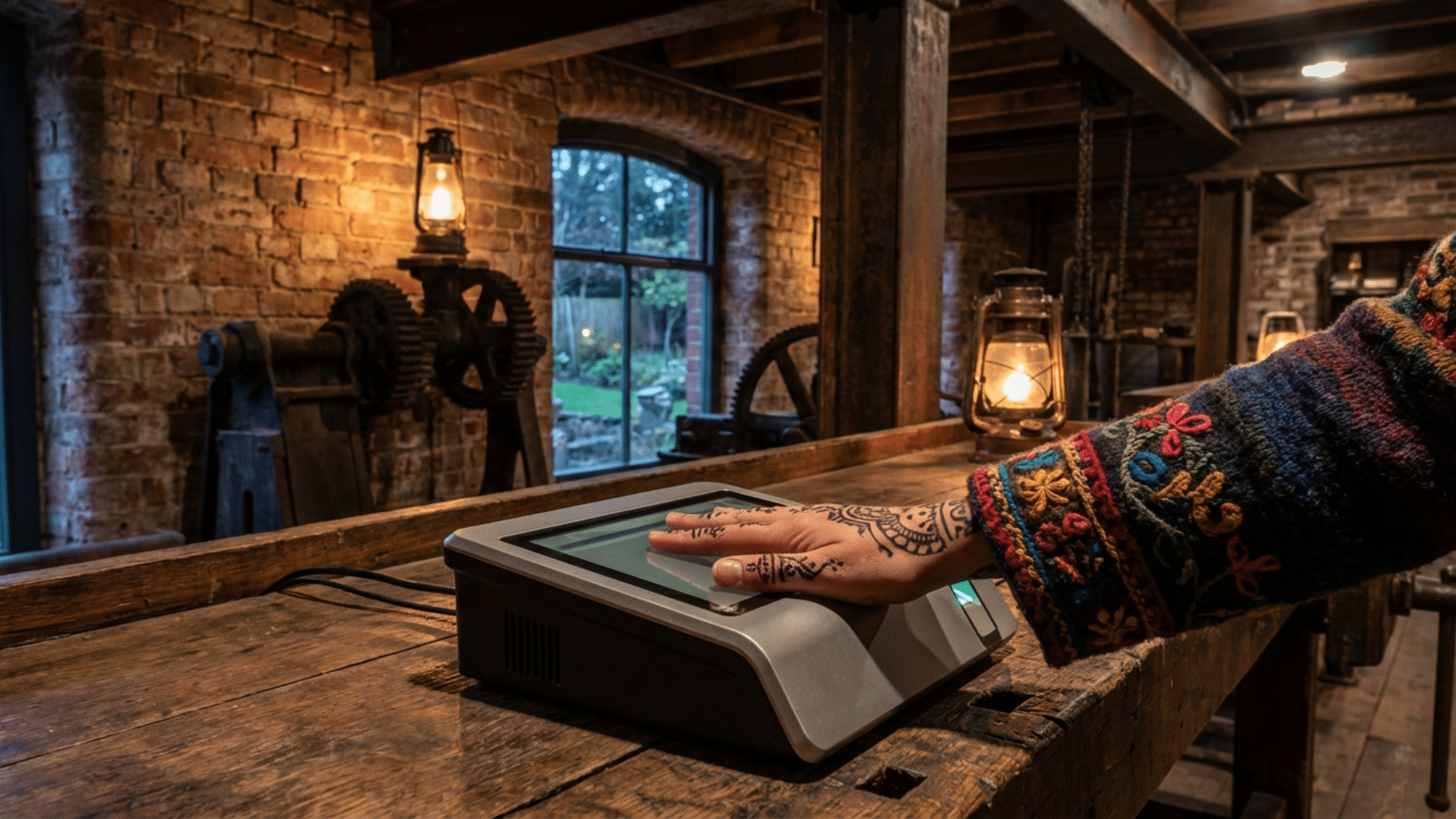
Biometric access control is one of them. It uses unique physical traits to verify identity more securely. This change is shaping modern security systems.
Understanding how it works and why it matters can help in making better decisions about safety and access contro.
What is a Biometric Access Control System?
A biometric access control system is a security system that uses a person’s unique physical traits to allow or deny access to a place or device.
Instead of relying on keys, cards, or passwords, it identifies individuals based on features like fingerprints, facial patterns, iris scans, or voice. These traits are difficult to copy, which makes the system more secure.
When a person tries to enter, the system scans their biometric data and compares it with stored information. If there is a match, access is granted. If not, entry is denied.
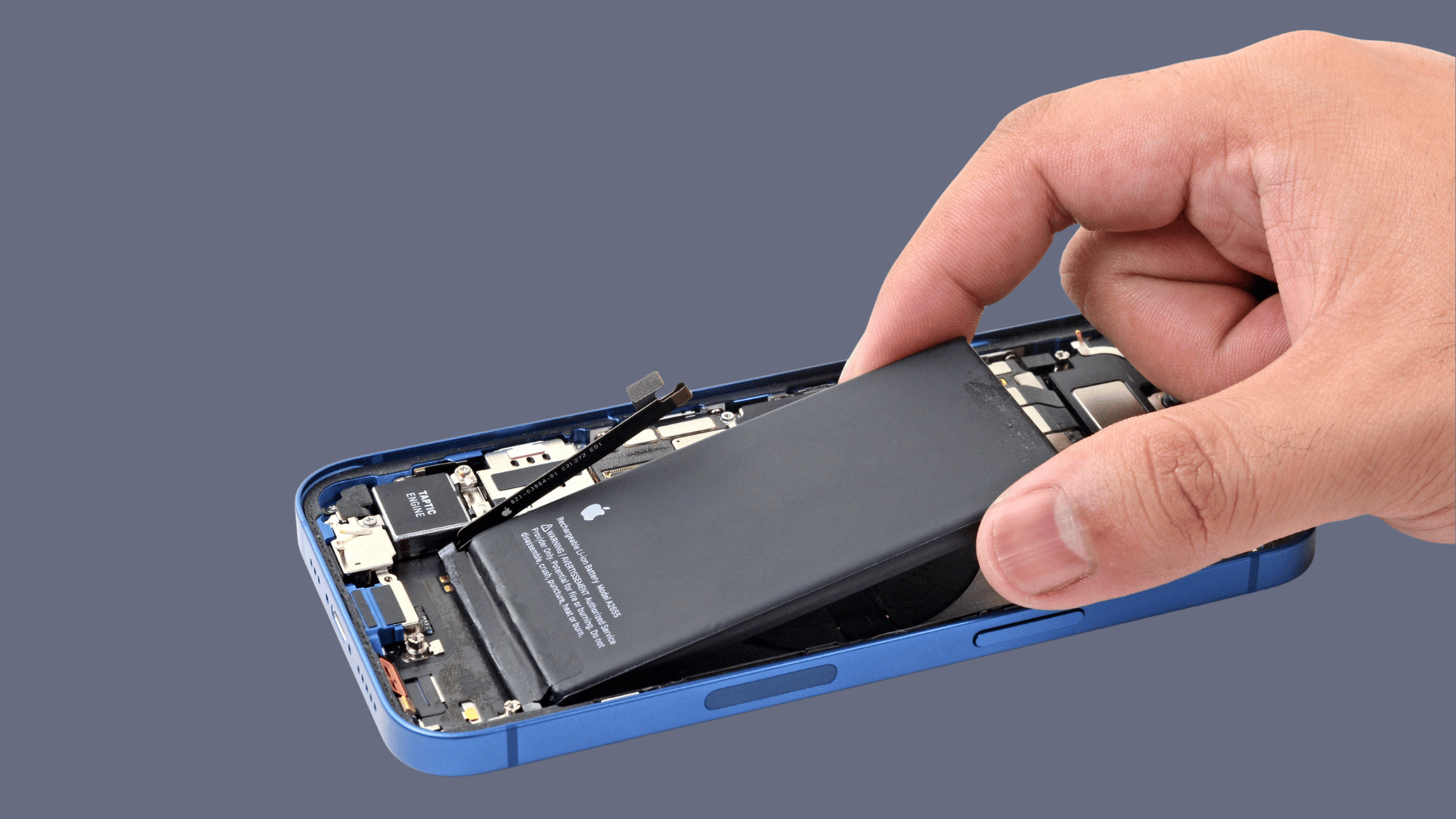
This type of system is widely used in offices, secure buildings, and even smartphones to improve safety and reduce the risk of unauthorized access.
How Does a Biometric Access Control System Work?
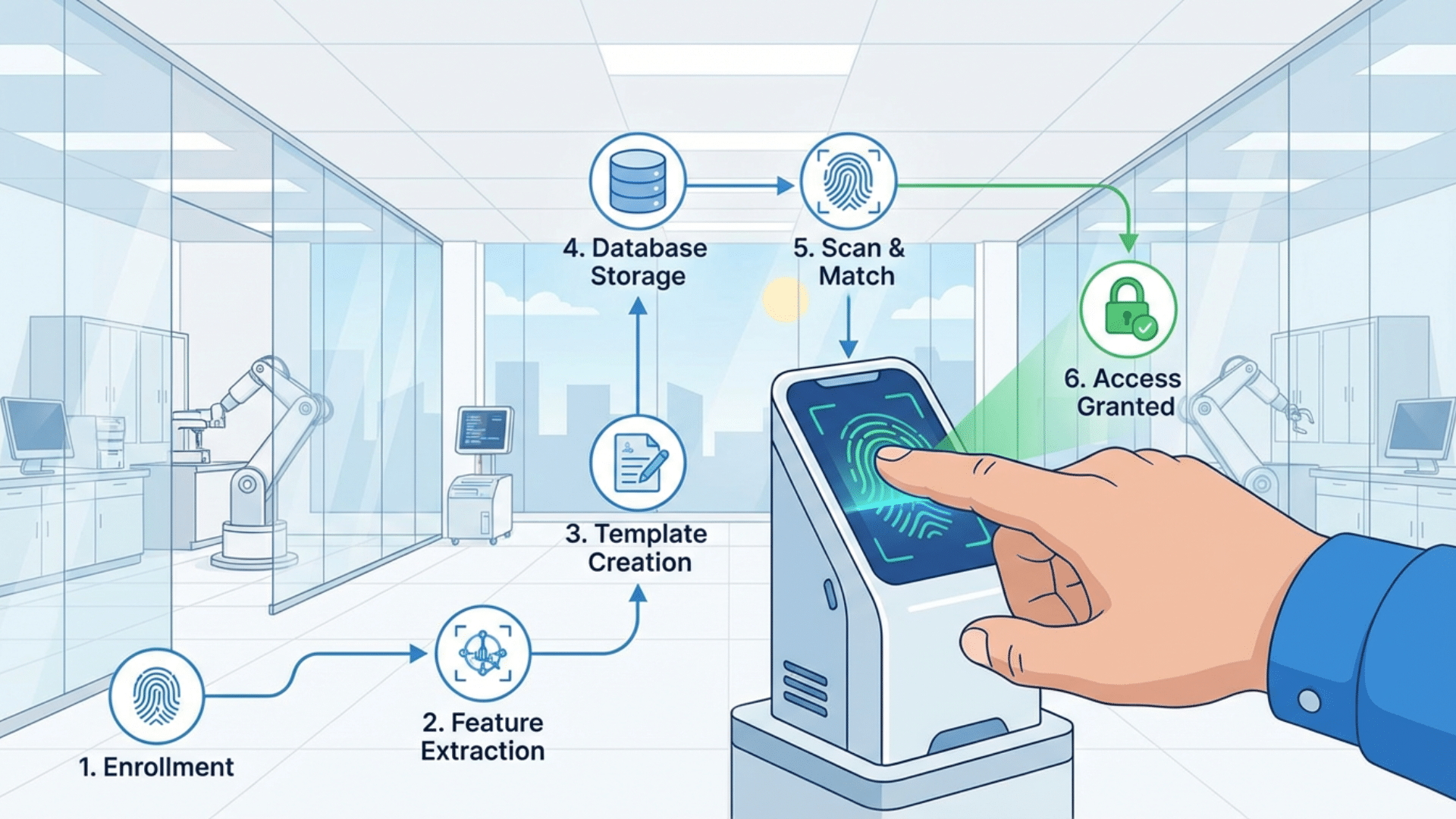
A biometric access control system works by identifying a person using their unique physical traits. It follows a clear process to check and confirm identity before allowing access.
1. Data Capture: The system first scans a biometric trait, such as a fingerprint, face, or iris, using a sensor or camera.
2. Data Conversion: The captured data is then converted into a digital format. This is not an image but a coded template based on unique patterns.
3. Data Storage: The system stores this template securely in a database or on a device. In most cases, it does not store raw images.
4. Matching Process: When a person tries to access again, the system scans their trait and compares it with the stored template.
5. Access Decision: If the data matches, access is granted. If it does not match, access is denied.
This process happens within seconds, making biometric systems both fast and reliable for modern security needs.
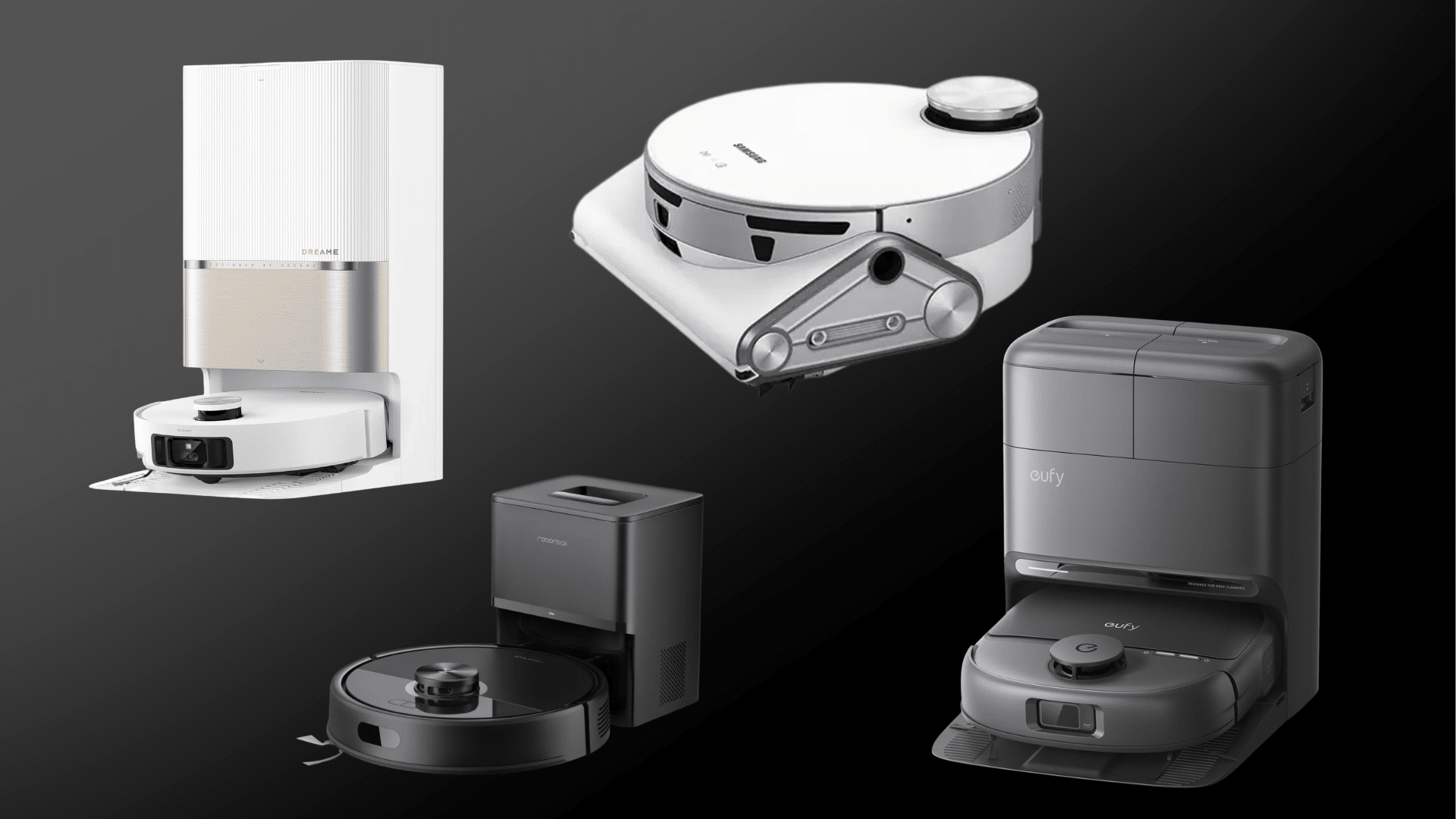
Types of Biometric Access Control Systems
Biometric access control systems use different human traits to verify identity. Each type works in its own way and is suited for specific security needs, environments, and levels of security.
Fingerprint Recognition

This is the most widely used biometric system. It scans the unique ridges and patterns on a person’s fingertip to identify them. The process is quick and usually takes only a second.
It is commonly used in offices, smartphones, and attendance systems. While it is affordable and easy to use, performance can sometimes be affected by dirt, moisture, or worn fingerprints.
Facial Recognition
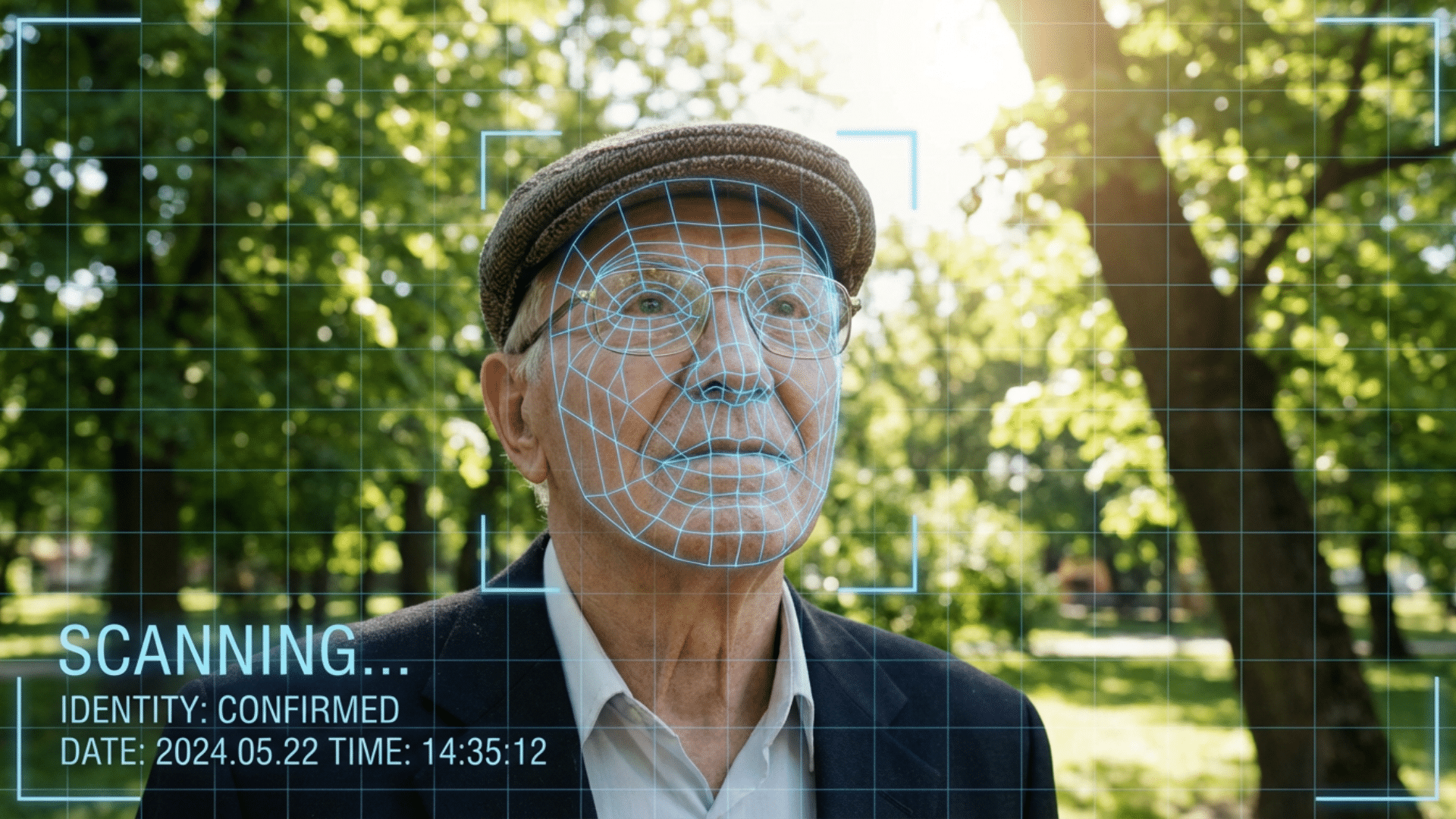
Facial recognition uses a camera to analyze key facial features, such as the distance between the eyes, nose shape, and jawline.
It allows users to gain access without touching any device, which makes it useful in busy or hygiene-sensitive environments. It is often used in airports, offices, and public buildings. However, lighting conditions and camera quality can impact accuracy.
Iris and Retina Scanning
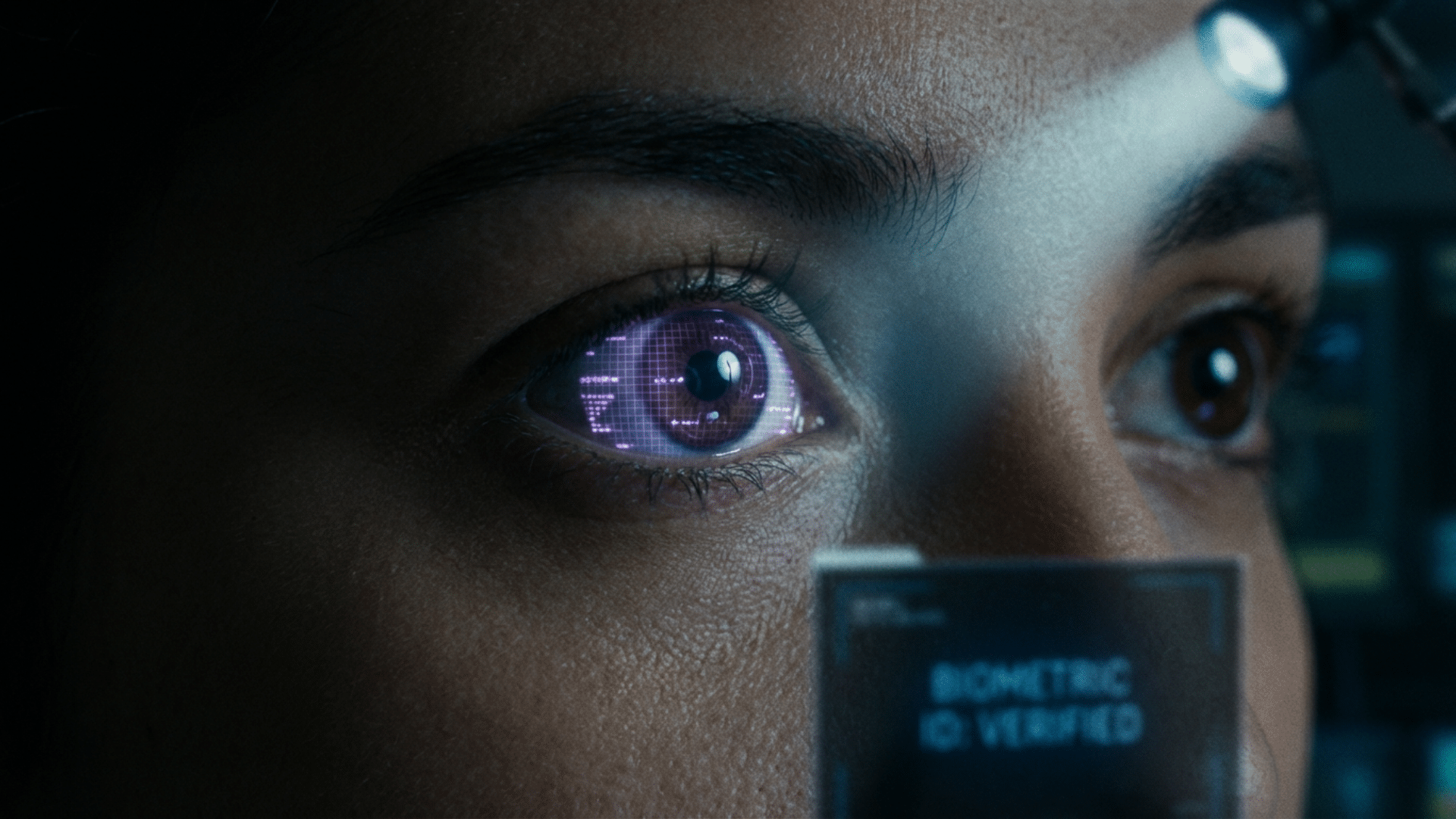
These systems focus on the eye, one of the most unique parts of the human body. Iris scanning captures patterns in the colored part of the eye, while retina scanning looks at blood vessel patterns at the back of the eye.
Both methods are highly accurate and difficult to fake. They are mainly used in high-security areas like research labs or government facilities due to their cost and precision.
Voice Recognition

Voice recognition systems identify a person based on speech patterns, tone, and rhythm. They are often used for remote access, phone-based systems, and smart assistants.
This method is convenient because it does not require physical contact. However, background noise, illness, or changes in voice can sometimes affect performance.
Hand Geometry Recognition
This system measures the shape, size, and structure of a person’s hand, including finger length and width. It is not as detailed as fingerprint or iris scanning, but it is still useful for basic access control.
It has been used in workplaces for time tracking and entry systems. It is reliable, though less common in modern systems.
Vein Recognition

Vein recognition uses infrared light to scan the pattern of veins inside a person’s hand or finger. These patterns are unique and located beneath the skin, making them very hard to copy or steal.
This method offers high security and accuracy. It is often used in banks, healthcare settings, and other areas where strong identity verification is required.
Key Features of Biometric Access Control Systems
Biometric access control systems include several advanced features that make them more secure and efficient than traditional methods. These features help improve accuracy, speed, and overall system reliability.
| Feature | Description |
|---|---|
| High Accuracy | Uses unique biological traits, reducing the risk of unauthorized access or identity errors. |
| Fast Authentication | Verifies identity in seconds, enabling quick, smooth entry without delays. |
| Secure Data Storage | Stores biometric data as encrypted digital templates instead of raw images for better protection. |
| Audit Trails | Keeps records of entry and exit times, helping track user activity and improve monitoring. |
| Contactless Options | Supports touch-free access, such as facial recognition, improving hygiene and convenience. |
| Integration Capability | Can connect with other security systems such as CCTV, alarms, and access management software. |
| User Management | Allows easy addition, removal, and control of users within the system. |
| Reduced Fraud Risk | Eliminates issues such as lost cards or shared passwords, reducing the risk of unauthorized access. |
| Scalability | Can be expanded to support more users or multiple locations as needed. |
| Real-Time Monitoring | Provides instant alerts and live tracking of access events for better control. |
Where are Biometric Access Control Systems Used?
Biometric access control systems are used in many places where security and controlled entry are important. Their ability to verify identity quickly makes them useful across different industries.
Offices and Corporate Buildings
Many companies use biometric systems to manage employee access. They help track attendance and prevent unauthorized entry into restricted areas.
Healthcare Facilities
Hospitals and clinics use biometric access controls to protect patient records and control entry to sensitive areas such as labs and storage rooms.
Banks and Financial Institutions
Banks rely on biometric systems to secure vaults, data centers, and customer transactions. This helps reduce fraud and improve safety.
Schools and Campuses
Educational institutions use these systems to manage student and staff access, improving overall campus security.
Residential Buildings
Apartments and gated communities use biometric systems for secure entry, replacing keys and access cards.
Government and High-Security Areas
Government offices, research labs, and military facilities use advanced biometric systems for strict access control and identity verification.
Biometric Access Control vs Traditional Access Methods
Biometric systems differ from traditional methods in how they verify identity and manage access. The table below highlights the key differences.
| Factor | Biometric Access Control | Traditional Methods (Keys, Cards, Passwords) |
|---|---|---|
| Security Level | High, based on unique traits | Lower can be copied or shared |
| Ease of Use | Simple, no need to remember or carry anything | Requires keys, cards, or passwords |
| Risk of Loss | No risk of losing access credentials | Keys and cards can be lost or stolen |
| Authentication Speed | Fast and automatic | May take longer to enter codes or use cards |
| Fraud Risk | Very low, hard to fake | Higher risk of duplication or misuse |
| Maintenance | Minimal, mostly digital management | Requires replacing keys, cards, or resetting passwords |
Challenges and Limitations of Biometric Systems
While biometric access control systems offer strong security, they also pose certain challenges that should be considered before use.
- Privacy Concerns: Biometric data is highly sensitive because it is linked to a person’s identity. If this data is misused or exposed, it can raise serious privacy issues.
- High Initial Cost: Installing biometric systems can be expensive. The cost includes hardware, software, and setup, which may not suit smaller businesses.
- Accuracy Issues: Although generally reliable, biometric systems can sometimes fail. Factors like poor lighting, dirt, injuries, or changes in appearance may affect accuracy.
- Data Security Risks: If the stored biometric data is hacked, it cannot be changed like a password. This makes secure storage and encryption very important.
- System Errors and Failures: Technical problems, power outages, or system malfunctions can prevent access, leading to delays or disruptions.
- User Acceptance: Some people may feel uncomfortable using biometric systems due to privacy concerns or lack of trust in the technology.
How to Choose the Right Biometric Access Control System
Choosing the right biometric access control system depends on your needs, budget, and the level of security required. A simple approach can make the decision easier.
First, consider how much security is needed. High-risk areas may require advanced systems such as iris or vein recognition, while smaller spaces can use basic options.
Next, think about the type of biometric method. Fingerprint systems are common and affordable, while facial recognition allows contactless use.
Budget is also important. It is necessary to balance the cost of installation with the cost of long-term maintenance.
The system should also work well with existing tools, such as cameras or alarms. Ease of use matters, as a simple system reduces errors.
Finally, robust data protection is essential to safeguard biometric information.
Conclusion
Biometric access control systems continue to gain attention as security needs become more complex.
With ongoing technological improvements, these systems are becoming more accurate, accessible, and easier to manage.
At the same time, careful planning is still important to ensure proper use and data protection.
Taking the time to evaluate available solutions can make a real difference in overall security. Review your needs today and consider if a biometric system fits your setup.
Frequently Asked Questions
Is Biometric Access Safe?
Biometric access is generally safe because it uses unique physical traits that are hard to copy. Most systems also encrypt data for added security.
Can Biometric Systems Be Hacked?
Biometric systems can be hacked, but it is more difficult than traditional methods. Strong encryption and secure storage help reduce this risk.
Which Biometric System is Best?
The best system depends on your needs and budget. Fingerprint is common, while iris or vein systems offer higher security.